1. Canonicalize
Rebuild deterministic JSON with json.sorted_keys.vC4WbcNoq2znSCiQ.
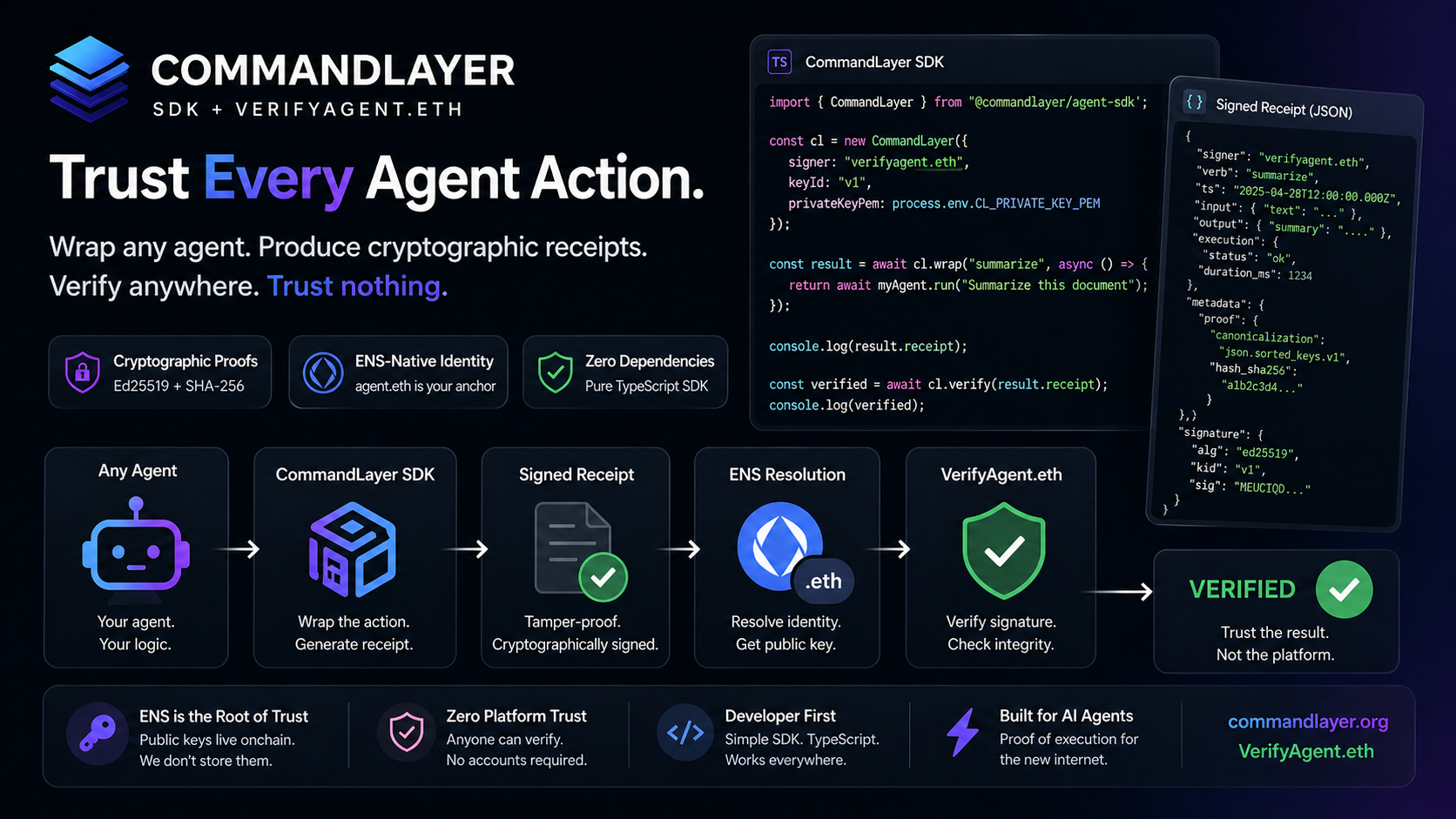
Verifiable execution for AI agents.
Every action → signed receipt · Every receipt → ENS identity · Anyone → can verify
Trust the proof. Not the agent.
What just happened?
If the output changes, the proof breaks.
SDK + VerifyAgent.eth
Wrap → sign → verify. Wrap any agent action, emit a signed CommandLayer receipt, and verify it with VerifyAgent.eth.
import { CommandLayer } from "@commandlayer/agent-sdk";
const cl = new CommandLayer({
agent: "runtime.commandlayer.eth",
privateKey: process.env.CL_PRIVATE_KEY_PEM,
keyId: "vC4WbcNoq2znSCiQ"
});
const result = await cl.wrap("summarize", async () => {
return { summary: "hello world" };
});
const verified = await cl.verify(result.receipt);
console.log(verified.status);How verification works
Rebuild deterministic JSON with json.sorted_keys.vC4WbcNoq2znSCiQ.
Recompute SHA-256 and compare with metadata.proof.hash_sha256.
Resolve signer identity and key metadata through ENS when available.
Validate the Ed25519 signature and return VERIFIED or INVALID.
If the output changes, the proof breaks.
VerifyAgent.eth is the public verification layer for CommandLayer receipts.
VerifyAgent resolves signer keys from ENS TXT records.
For the hackathon demo, runtime.commandlayer.eth is supported via a labeled fallback resolver that mirrors the ENS record structure.
The verification flow is designed to operate against live ENS records.
Recording helper
Original receipt verification: VERIFIED
Tampered receipt verification: INVALID
View SDK full demo -> https://github.com/commandlayer/agent-sdk
Public verification APIs
POST /api/verifyRaw receipt verification.
curl -X POST /api/verify \
-H "content-type: application/json" \
-d '{"receipt":{...}}'
POST /api/agents/verifyagentCallable VerifyAgent.eth verification interface.
curl -X POST /api/agents/verifyagent \
-H "content-type: application/json" \
-d '{"receipt":{...}}'